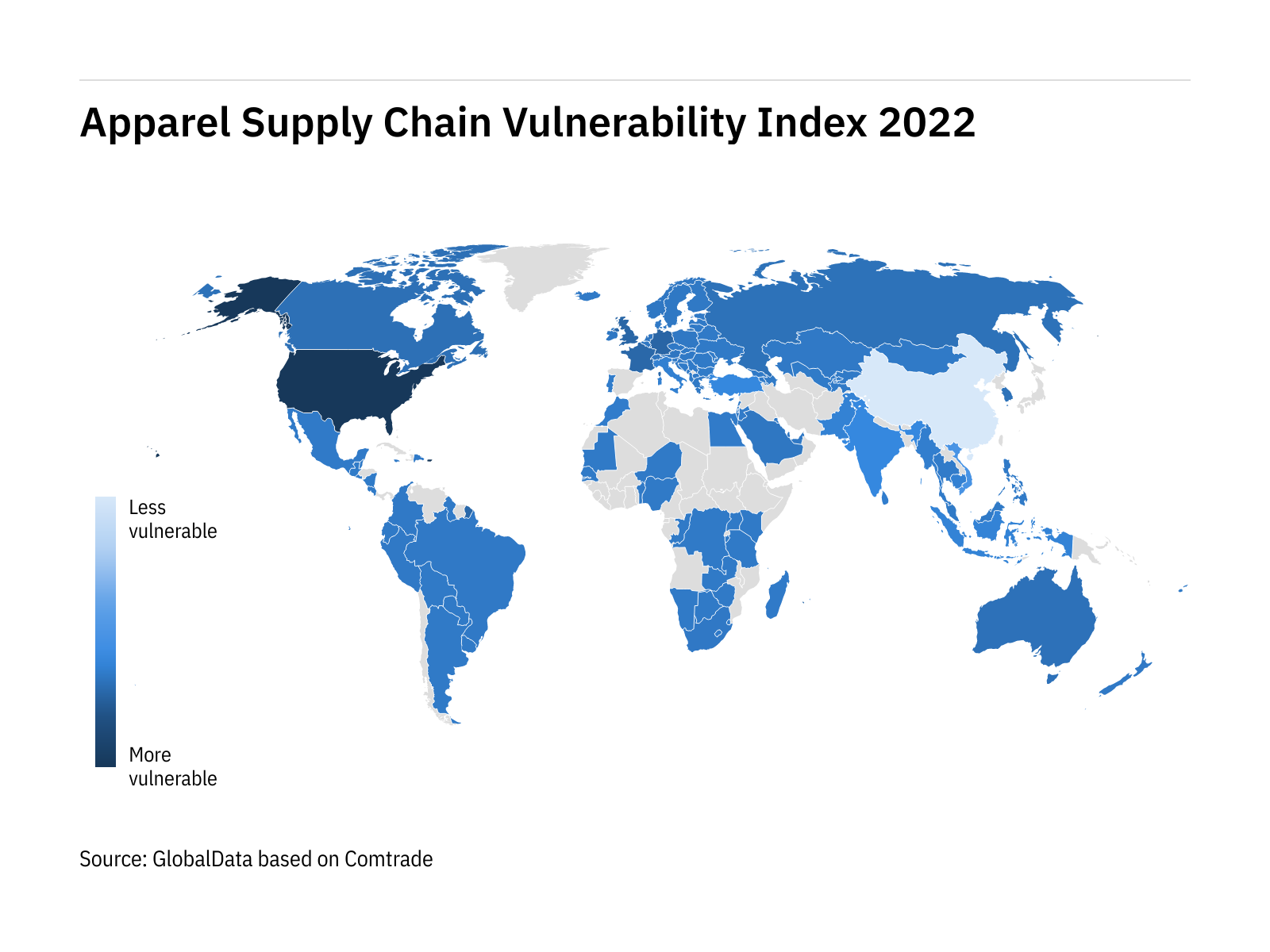
China's resilience shines through in index of world's most vulnerable apparel supply chains - Just Style
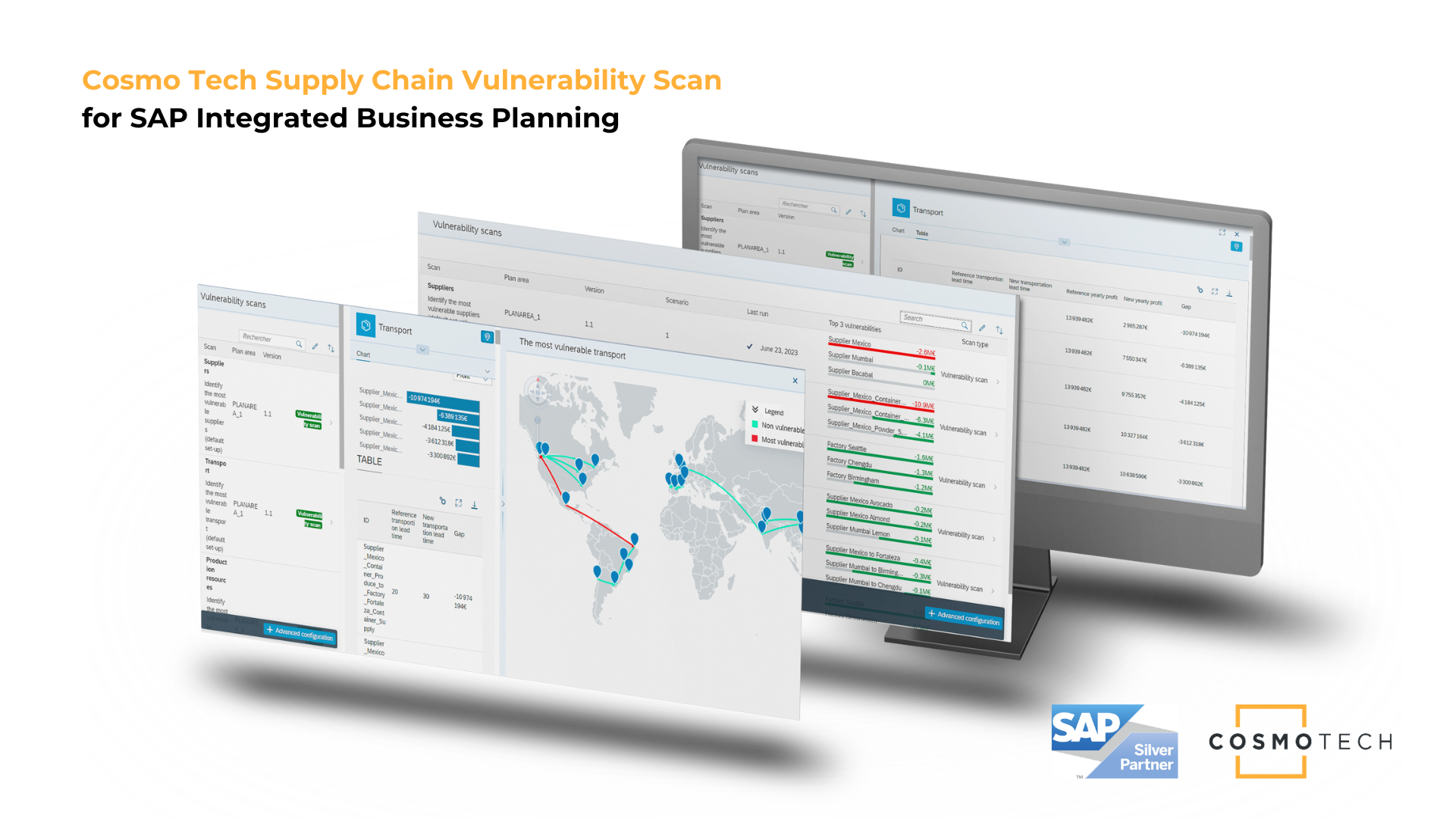
The Supply Chain Vulnerability Scan from Cosmo Tech is now Available on the SAP® Store | Business Wire

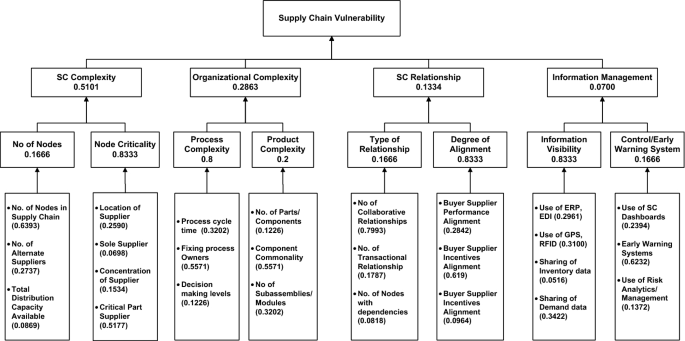
Minimizing the vulnerabilities of supply chain: A new framework for enhancing the resilience | Semantic Scholar

Amazon.com: Managing Supply Chain Risk and Vulnerability: Tools and Methods for Supply Chain Decision Makers: 9781848826335: Wu, Teresa, Blackhurst, Jennifer Vincent

Buildings | Free Full-Text | Resilient Capabilities to Tackle Supply Chain Risks: Managing Integration Complexities in Construction Projects
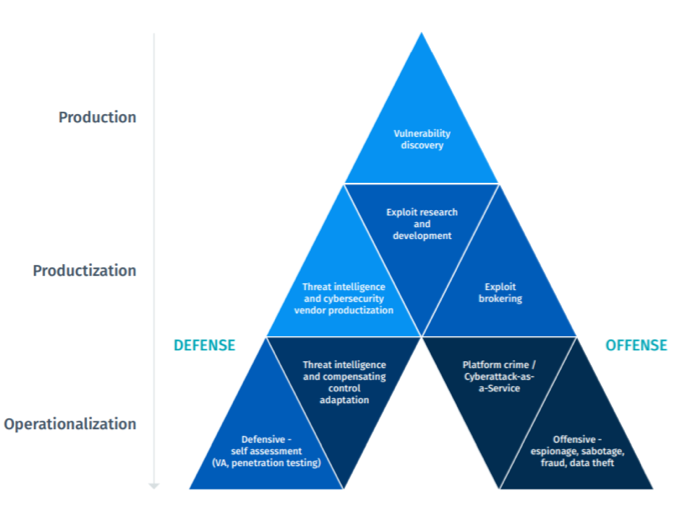
PPT - Supply Chain Vulnerability, Risk, Robustness & Resilience PowerPoint Presentation - ID:9092466